Consistently superior protection, combined with risk management and vulnerability assessment
A single console gives you comprehensive protection for your workstations and servers (physical or virtual) and also keeps you informed on the risk factors by discovering and prioritizing risky OS and software misconfigurations.
Best Protection, Best Performance
- GravityZone is constantly ranked #1 in independent security tests, providing trusted security for companies of all sizes.
Comprehensive Security and Efficient Management
- All security activities, including working with the Endpoint Risk Management dashboard are managed from a single console and single agent.
Full Control and Enhanced Business Productivity
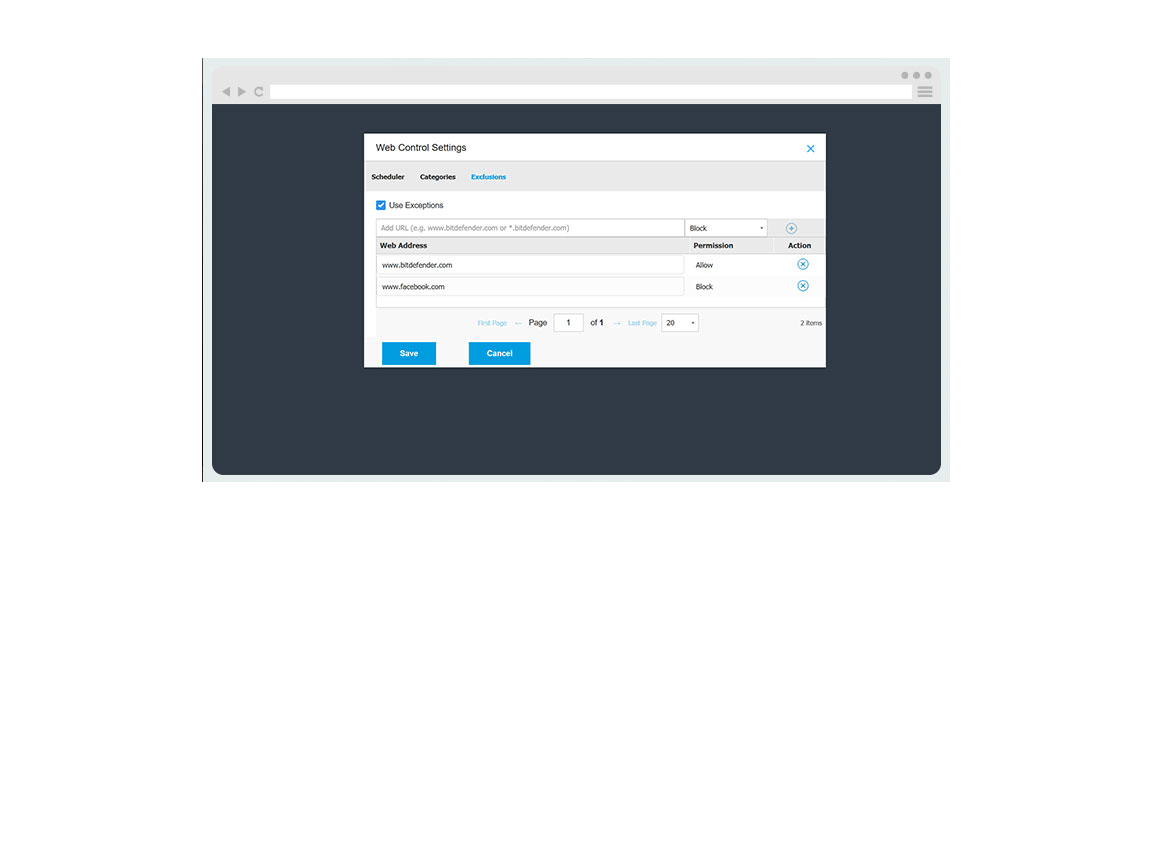
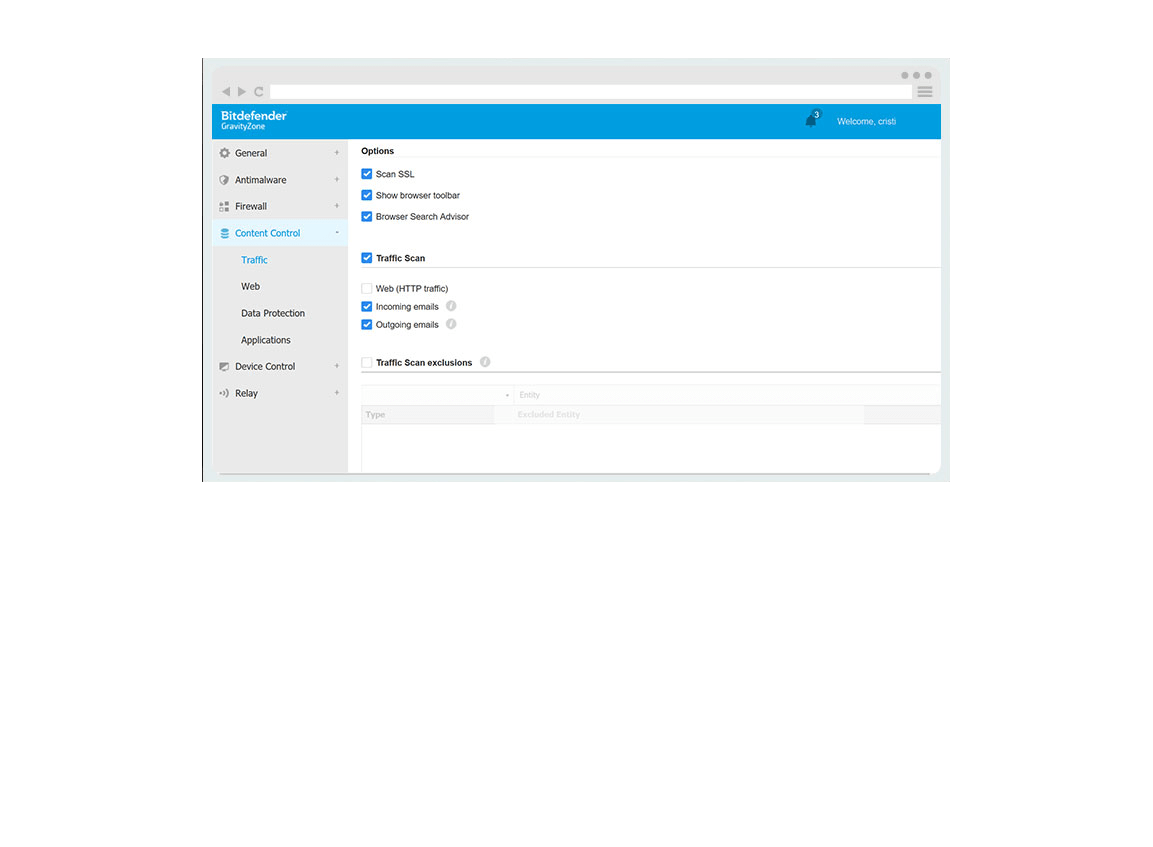
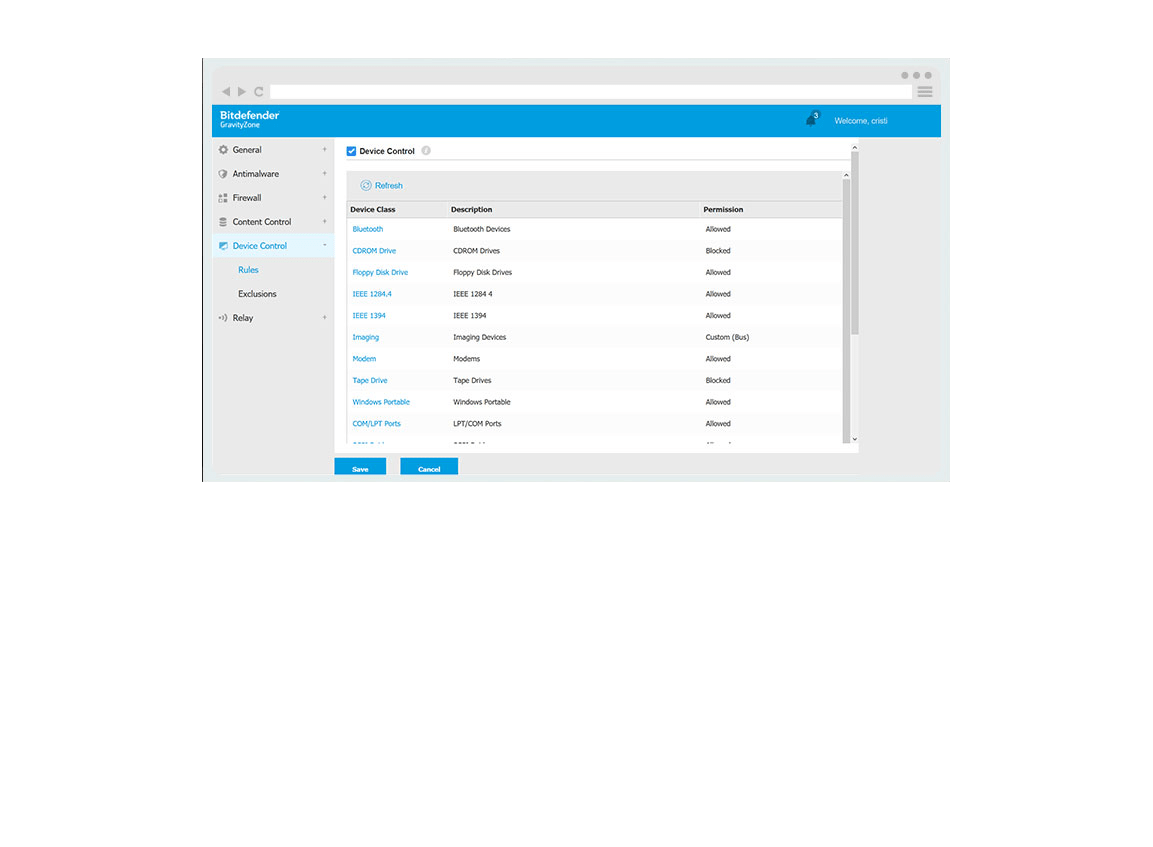
- Grant or deny access to websites and applications through highly granular security controls to ensure maximum protection and minimum effort.
NEW Network Attack Defense
Get a new level of protection against attacks aiming to gain access to the system by exploiting network vulnerabilities.
Extend protected areas, now with network based security that blocks threats like Brute Force attacks, Password Stealers, Network Exploits, lateral movements before they can execute.
Layered Protection For Your Endpoints
Your desktops, laptops and servers are protected with layered security: machine learning, heuristics, signatures, memory protection and continuous monitoring of running processes, malware blocking, disinfect, quarantine and rollback.
Web-based Security – No Need For Hardware
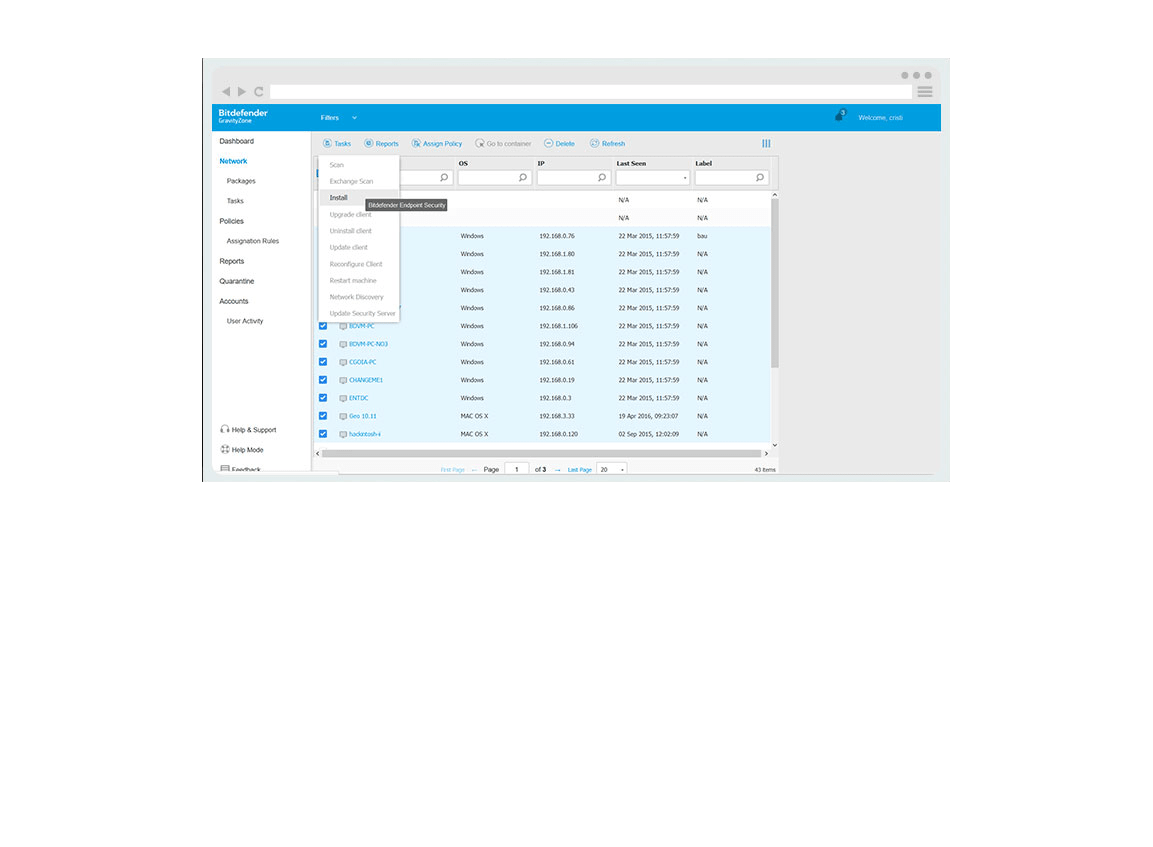
There will be no need for dedicated servers or more IT staff, as GravityZone centralizes all security features into a single console. Employees never have to update or monitor security activities. You can save time by remotely installing protection on all unprotected computers through a simple and comprehensive procedure. The security solution can be deployed either on premises or hosted by Bitdefender in cloud.
Protection integrated with Endpoint Risk Management
Effectively identifying, assessing, and remediating endpoint weaknesses is pivotal in running a healthy security program and reducing organizational risk. Endpoint Risk Management is an infrastructure for reducing exposure and hardening endpoint surface area, by discovering and prioritizing risky OS and software misconfigurations. Administrators are now able to address the vulnerabilities using this interface.
AI And Machine Learning Perfected Over Years
Artificial Intelligence and machine learning are essential to combat a threat landscape that is larger and more sophisticated than ever. Unlike other vendors, Bitdefender has years of experience perfecting these technologies and the results clearly show this: better detection rates with fewer false positives.
Largest Security Intelligence Cloud
With over 500 million machines protected, the Bitdefender Global Protective Network performs 11 billion queries per day and uses machine learning and event correlation to detect threats without slowing down users.
Advanced Application Behavior Monitoring
Bitdefender’s Process Inspector permanently monitors running processes for signs of malicious behavior. A pioneering and proprietary technology launched in 2008 as (AVC), it has constantly been enhanced, keeping Bitdefender one step ahead of emerging threats.
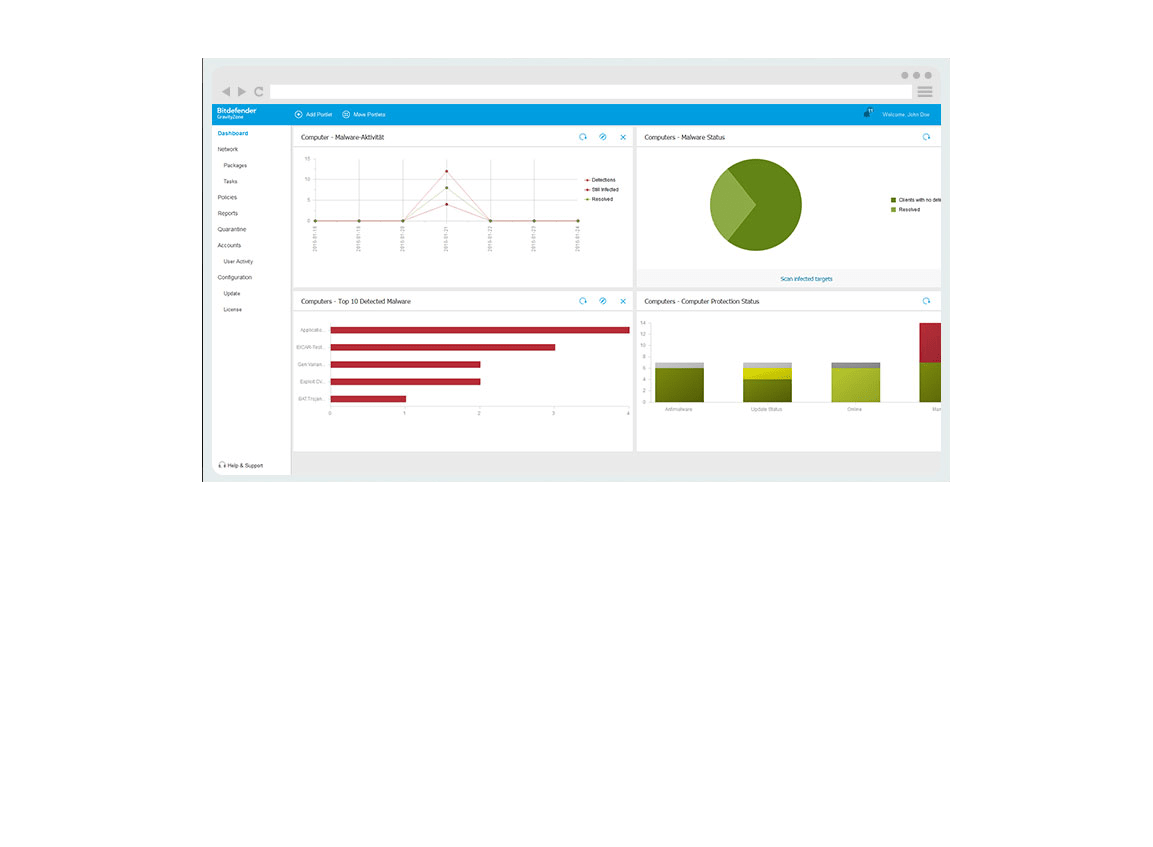
One Console for All Your Events and Reports
Easily track all security events in your organization
Reports and alerts help you be on top of any business security event
Avoid losing data and confidential information
Block hackers from trying to steal sensitive records or employee information
Simple remote deployment
Save time by remotely installing protection on all computers that are unprotected
Enhance your business productivity
Control employee access to certain websites or applications
Highly granular security controls
Customize every aspect of security to ensure maximum protection and minimum effort
Bitdefender layered next generation endpoint protection platform
Uses adaptive-layered architecture that includes endpoint controls, prevention, detection, remediation and visibility.